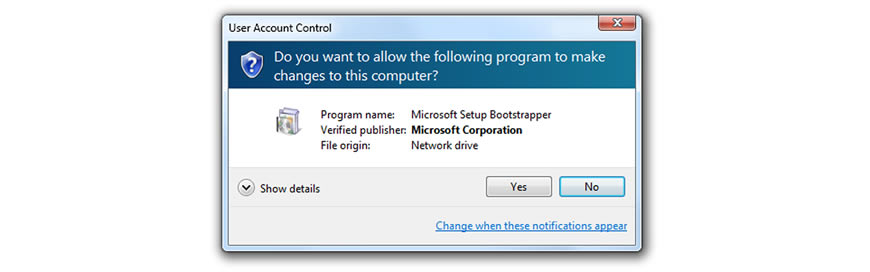
A new major vulnerability has been discovered that allows anyone to gain privilege escalation access to windows. This can be a major issue as normally the user has to be an administrator and allow escalated access to the computer. This vulnerability was discovered in Windows Task Scheduler.
Sales Inquiries: (336) 313-2841 | Current Clients: (336) 310-0277
Blog
Why you need Hardware-as-a-Service
The new flashy set of PCs your company just bought last year are becoming outdated, and you don’t have enough IT staff to maintain them. If this is your current situation, it might be time to consider Hardware-as-a-Service (HaaS), a pay-as-you-go model where you pay your managed services provider (MSP) a monthly fee to take care of all your hardware needs.
Hybrid cloud: Give your SMB more flexibility
How To Make Sure You Never Fall Victim To Ransomware
Make tech trends work for you! Here‘s how
PhishPoint attack looks like SharePoint

Have you ever received an email that claimed to come from a bank or government office when it obviously didn’t? It was probably a phishing scam trying to trick you into downloading malware. The most recent campaign duplicates a trustworthy Office 365 email and can fool even the most skeptical users.
What are the risks of BYOD?
The convenience of dual monitors
4 Questions You Should Ask Any IT “Expert” Before Letting Them Touch Your Network

As businesses have become ever more dependent on technology, IT services providers have been popping up left and right. They’ve all got different strengths, capabilities and price points to consider. Some charge you by the hour and, while available to address any concerns you may have, they are pretty hands-off.
4 E-mails You Should NEVER Open

No matter how “bomb-proof” we make your network, you and your employees can still invite a hacker in if you click on a link or open an attachment in an e-mail sent by a cybercriminal. Some spam is obvious (can you say, “Viagra at a discount”?) but others are VERY cleverly designed to sneak past all the filters and trick the recipient into opening the door.